In addition to federal requirements, the three types of safeguards under the HIPAA Security Rule play an important role in securing sensitive health information and restricting unauthorized access to health data. The HIPAA Administrative Safeguards make up over half of the Security Rule requirements and are a critical component to the security of larger health data.
However, not every type of administrative safeguards will necessarily apply to all healthcare organizations. Similarly, the HIPAA physical and technical safeguards can vary, and every organization will need to review their policies, workflow, and security needs to ensure that the appropriate measures are in place. This article outlines the key HIPAA Administrative Safeguards and how HIPAA Ready can streamline your efforts to maintain confidentiality, security, and integrity of electronic protected health information (ePHI).
What are the HIPAA Administrative Safeguards?
The administrative safeguards under the HIPAA Security Rule involve developing and implementing processes, policies, and procedures that will work best in protecting against unwanted breach and unwanted disclosure of sensitive health information.
HHS defines administrative safeguards as “administrative actions, and policies and procedures, to manage the selection, development, implementation, and maintenance of security measures to protect electronically protected health information and to manage the conduct of the covered entity’s workforce concerning the protection of that information.”
Essentially, covered entities as well as their business associates must implement clear guidelines for their employees specifying the correct use and care of ePHI to protect against unwanted breaches. HIPAA Administrative Safeguards lay the foundation for compliance with the technical and physical safeguards that follow.
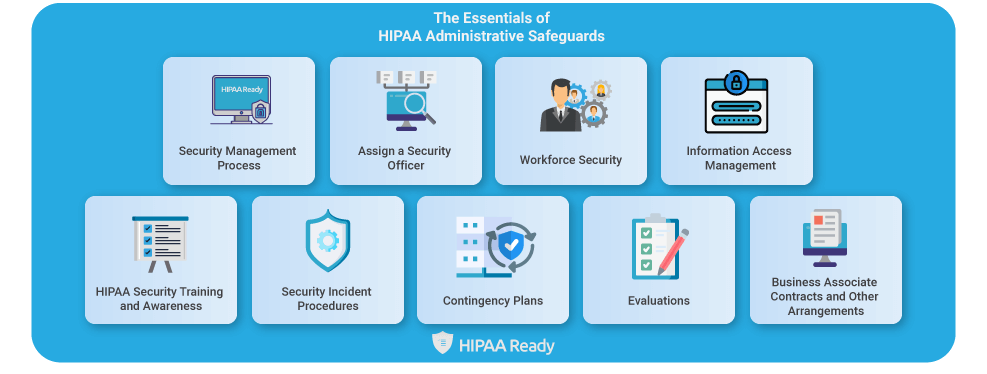
The Essentials of HIPAA Administrative Safeguards
Security management process
Covered entities and business associates that handle or encounter must have a strong strategy in place that will prevent, detect, and contain any vulnerabilities that can compromise the integrity and confidentiality of ePHI. In other words, developing and implementing clear policies and procedures to guide employees in HIPAA administrative safeguard compliance. This is where organizations need to consider their risk analysis and risk management procedures. For instance, identifying potential vulnerabilities to ePHI and how likely a breach will take place, how to best mitigate those risks, and creating internal policies to penalize employees who are found to violate the rules. With HIPAA Ready, users can streamline this process by easily adding, editing, or updating new HIPAA policies and notifying relevant individuals across the organization.
Assign a Security Officer
The law requires that covered entities assign security responsibilities to an individual for the development of security policies and procedures. Large organizations may have multiple people managing security or an entire dedicated team because they have multiple locations. In smaller organizations, the privacy and security officer’s role may be assigned to a single individual. However, it is not necessary to hire someone from outside the organization. It can be a qualified individual from within the organization. The Security Rule was made flexible as each organization will have different requirements. The security officers should reflect the size, complexity, and technical capabilities of the business. With our software, officers can easily monitor and manage all compliance-related tasks from anywhere.
Workforce Security
This step involves determining which employees are authorized to access ePHI so that they can perform their job functions properly. In simple words, employees who can perform their jobs without access to ePHI should not be able to view personal health information. This is where termination procedures must be taken into account. For instance, deactivating passwords or access codes after an employee who had access to ePHI has been terminated. To make things easier, within HIPAA Ready, users can maintain a logbook of all the employees and the level of access to ePHI granted to each of these employees, including to whom each ePHI containing device is assigned.
Information access management
This step reiterates the above-mentioned point that pertains to restricting access to ePHI. Only minimal access to ePHI should be given to an employee to carry out their job functions. The following specifications must be implemented in the policies and procedures:
- Authorization and Supervision – § 164.308(a)(3)(ii)(A)
- Workforce Clearance – § 164.308(a)(3)(ii)(B)
- Termination Procedures – § 164.308(a)(3)(ii)(C)
HIPAA Security Training and Awareness
Whether it’s training or work operations, organizations should streamline their workflows to reduce administrative burdens and save valuable time. If you operate within the healthcare industry, there is no need to remind you of the importance of security training. However, the following four components are the standard HIPAA administrative safeguard training requirements:
- Periodic Reminders of the Importance of Security – § 164.308(a)(5)(ii)(A)
- Protections for Malicious Software – § 164.308(a)(5)(ii)(B)
- Log-in Monitoring – § 164.308(a)(5)(ii)(C)
- Password Management – § 164.308(a)(5)(ii)(D)
With HIPAA Ready, users can add new training courses, assign a trainee, set a training schedule, and set details of the training effortlessly.
Security Incident Procedures
The purpose of this standard requires covered entities to develop clear policies and procedures in place that addresses security incidents. The policies should outline the procedures that must be taken in the event of a security incident. Essentially, all the employees must understand how they will reach in the event of each type of breach to ePHI. This safeguard requires one specification: Response and Reporting – § 164.308(a)(6)(ii)
Contingency Plans
The purpose of this step is to develop strategies for recovering access to ePHI in the event of a natural disaster or other occurrences, such as a power outage. There are five standard specifications under contingency plans:
- Data Backup Plan – § 164.308(a)(7)(ii)(A)
- Disaster Recovery Plan – § 164.308(a)(7)(ii)(B)
- Emergency Mode Operation Plan – § 164.308(a)(7)(ii)(C)
- Testing and Revision Procedures – § 164.308(a)(7)(ii)(D)
- Application and Data Criticality Analysis – § 164.308(a)(7)(ii)(E)
Evaluations
Organizations need to know whether the implemented policies and procedures are adequately protecting their ePHI or not. Organizations must periodically review their strategies so that they can be adjusted to any environmental or operational changes that affect the security of ePHI.
Business Associate Contracts and Other Arrangements
Finally, organizations will need to sign a Business Associate Agreement (BAA) with any external entity that creates, receives, stores, or transmits ePHI on their behalf. It is mandatory to have a written contract or other arrangements in place that meets the applicable requirements of HIPAA. A covered entity may have hundreds of business associates, and maintaining proper records for each of them can be a difficult task. With our software, users can manage vendor agreements and print out readily available forms. Maintaining records in a single centralized space makes it easier to access or review contracts when required.
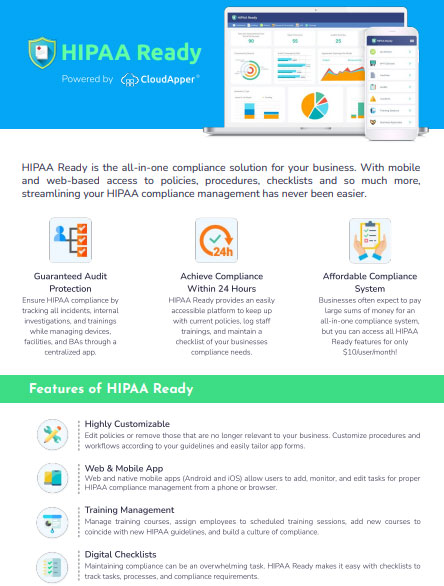
HIPAA Ready by CloudApper
With the ambiguity in the application of the HIPAA Rules, managing compliance tasks can be a daunting and frustrating task. Our HIPAA compliance management application was built for the sole purpose of reducing complexities and administrative burdens. With our solution, you will be guided in the right direction to ensure that your organization keeps on top of all the HIPAA requirements. Leave a comment to know more about HIPAA Ready.