Medical institutions are obliged to comply with the HIPAA rules and regulations that aim to protect a patient’s health information. However, even after imparting training to the employees and taking appropriate measures, cases of HIPAA violations surface every year. Read this checklist to make sure you are not missing or violating any HIPAA rules and regulations.
What is HIPAA?
The U.S. Department of Health and Human Services (“HHS”) issued the Privacy Rule to implement the requirement of the Health Insurance Portability and Accountability Act of 1996 (“HIPAA”). The Privacy Rule standards address the use and disclosure of an individual’s health information” – called “protected health information” by organizations subject to the Privacy Rule – called “covered entities”, as well as standards for individual’s privacy rights to understand and control how their health information is used. In layman’s terms this rule protects the privacy of a patient’s personal and health information by ensuring the following three types of protective measures:
Technical Protections
Scramble
Encrypt any ePHI outside the firm’s firewalled hard-ware. (Must do)
Control Access
Assign each user a centrally-controlled unique username and PIN code. Establish emergency procedures to govern ePHI release or disclosure. (Must do)
Authenticate ePHI
Protect data from corruption and incorrect destruction. (Or alternative)
Become Scramble-Ready
All devices that access the system should be able to encrypt and decrypt messages. (Or alternative)
Control Activity Audits
Log any access efforts and data manipulation. (Must do)
Enable Automatic Logoff
Log people out after a set time-frame. (Or alternative)
Physical Protections
Control facility access
Carefully track all individuals who have physical access to data storage, even cleaning staff. Take reasonable steps to block unauthorized entry. (Or alternative)
Manage Workstations
Write a policy to limit which workstations can access health data, guard screens from parties at a distance, and delineate proper workstation use. (Must do)
Protect Mobile
Remove data from devices before they are circulated to another user. (Must do)
Administrative Protections
Administrative actions, and policies and procedures, to manage the selection, development, implementation, and maintenance of security measures to protect electronically protected health information and to manage the conduct of the covered entity’s workforce in relation to the protection of that information.
- Security management process
- Assigned security responsibility
- Workforce security
- Information access management
- Security awareness and training
- Security incident procedures
- Contingency plan
- Evaluation
- Business associate contracts and other arrangements.
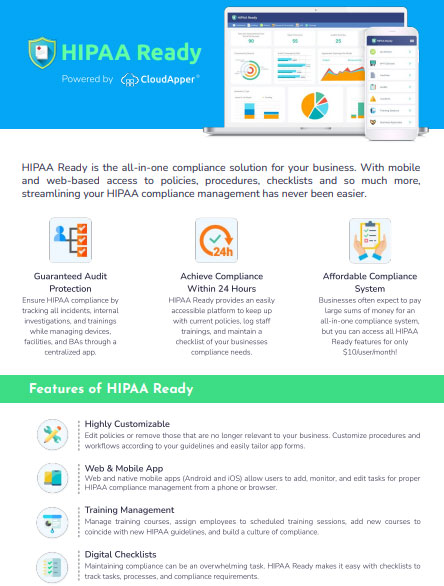
Worried about your organization’s compliance risk in terms of protecting health data? At CloudApper, we have developed HIPAA Ready – an app that not only helps you to protect your organization’s data but also offers a modern, affordable, and effective way of safeguarding yourself from the next HIPAA Compliance audit.