In this article, we will share some tips regarding HIPAA compliance to build your knowledge. The article offers insights into how an organization can translate its understanding of HIPAA into operational policies and procedures and achieve effective governance.
To establish strong and effective governance, all organizations need effective policies and procedures. The policies and procedures need to closely mesh with the compliance requirements specific to the organization’s nature and system.
So here are some tips to help you develop well-thought-out policies and procedures which will help you address HIPAA compliance in a structured and proactive manner.
Fundamentals of an Effective Compliance Program
The Office of the Inspector General (OIG) for the Department of Health and Human Services (HHS) released a compliance training guide and established ‘The Seven Fundamental Elements of an Effective Compliance Program.’ They are:
- Implementing written policies, procedures, and standards of conduct
- Designating a compliance officer and compliance committee
- Conducting effective training and education
- Developing effective lines of communication
- Conducting internal monitoring and auditing
- Enforcing standards through well-publicized disciplinary guidelines
- Responding promptly to detected offenses and undertaking corrective action
Document All Developments in Policies, Procedures, and Training
HIPAA-obligated organizations must document all the changes made to policies, procedures, and training schemes, including all other efforts taken. HIPAA Ready can serve as a great platform where you can document all the changes. These documentations are critical for HIPAA investigations.
Protect All Systems That Contain ePHI
If you are not sure where ePHI resides within your systems, it is better to be safe than sorry. Although, a risk analysis should’ve detected where all the ePHI is located within the environment. In case, it does not, you should assume that all systems in the environment are within the scope of HIPAA. There should be proper security safeguards in place and appropriate procedures specified within the policies. Listing all the places where ePHI resides is also made easy with HIPAA Ready.
A Risk Assessment Should Be Followed Up with a Comprehensive, Effective Risk Management Strategy
All risks identified during the risk analysis should be reduced to a reasonable and acceptable level. The risks must be subject to the risk management process because it is critical to the security of PHI and ePHI and is fundamentally required by the HIPAA Security Rule.
Construct an Airtight BYOD Policy
Bring Your Own Device (BYOD) is a practice that has been popular lately. But it’s more than just employees bringing in their privately owned devices into the workplace. It also includes company work phones and laptops that employees carry out of the office which are connected to a public or home network. There should be a comprehensive policy in place outlining the proper use of personal devices used for accessing PHI. Also, it’s best to encrypt all ePHI.
Execute a Post-Audit Remediation Plan
After conducting self-audits, covered entities and business associates must implement remediation plans to mitigate gaps in compliance and reverse compliance violations. The plans must be documented along with the intended dates the gaps will be remedied.
Have an Incident Response Plan
Regardless of whether you have already experienced a breach or not, you must have a response plan. If you are not prepared for the aftermath, it is going to be more expensive and challenging for your organization. The plan must be documented and used in the event of an incident to mitigate the potential impact. This way, you will also be able to reduce fines and negative impacts.
Anticipate Where and How a Breach Might Occur
Take note of common patterns and themes in the breaches that occur inside and outside of healthcare. Assess your own IT environment and try to find out if similar conditions exist and are ripe for exploitation. HIPAA training can be effective to educate employees on how to identify potential threats and security issues.
Learn the Differences between “Addressable” and “Required” Security Safeguards
Not all security measures will be appropriate for your organization. But in practice, all the security safeguards are required unless it can be justified rationally that the safeguards are not reasonable and appropriate for your organization. In this case, an appropriate alternative to the safeguard that achieves the same objectives must be put in place.
Get Help from the Outside
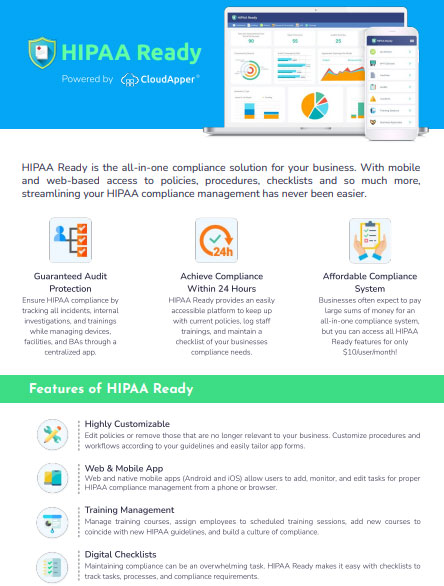
An instance of a HIPAA violation can be very costly for your business. Understandably, complying with the HIPAA law can be arduous. And that is where we come in.
Following these simple tips will be helpful to establish a better HIPAA compliance program. Everything discussed above can be streamlined using HIPAA Ready, a robust cloud-based HIPAA compliance software. With HIPAA Ready, you won’t need tons of paperwork. Instead, you can document all the activities and record all your efforts in HIPAA Ready.