From automating a variety of tasks for practices to providing better patient care, electronic health records (EHR) have many advantages. However, electronic health records are not exempt from risks. As the value of healthcare data remains high, protecting electronic health records has become even more challenging. Despite the effort healthcare organizations are making, the number of electronic health records being lost, stolen or compromised keeps increasing year after year.
In 2019 alone, 41.2 million healthcare records were reported to be stolen, exposed, or impermissibly disclosed. While some may be related to internal data breaches, healthcare organizations have also become one of the prime targets for cybercriminals. Some research suggests that a single EHR may be worth up to $1000 on the black market, which is why cybercriminals look to make profits from compromised patient data.
Organizations should take proactive measures to ensure that sensitive data is not readily available for cybercriminals and to also protect them from internal threats. Here are five tips for protecting your electronic health records from external, as well as internal threats:
Performing Regular Risk Assessments
Routine risk assessments should not be underestimated. Healthcare is an ever-evolving industry and organizations are constantly changing, and these changes should be assessed for the risks they present. For example, your office might have moved to a new location, upgraded software, and hardware, or changed EHR vendors – all these changes bring in new risks that should be properly assessed.
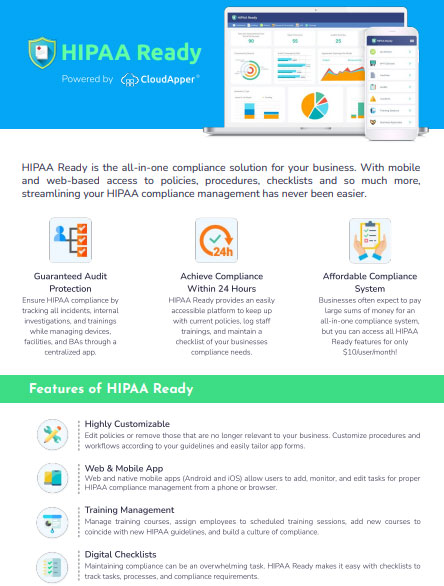
Risk assessments not only help you to identify security gaps in your organization’s physical, technical and administrative safeguards, but they are also required for HIPAA compliance and can potentially save your company from devastating data breaches. Understandably, performing risk assessments can be an arduous process but with the right tools like HIPAA Ready, you will not only be able to perform risk assessments promptly but also save time and money you spend by hiring third party vendors to conduct these assessments.
Biometric Patient Identification and Regular Patch Updates
Cybercriminals often wreak havoc by exploiting out of date or unpatched software, operating systems, and medical devices. Yet a surprising number of healthcare organizations are running outdated and common operating systems, such as Windows and Linux, making them susceptible to cyber-attacks. One of the most effective ways for protecting your electronic health records is to keep your software updated and fully patched, which includes medical devices.
Also, a surprising number of healthcare providers have been using biometric patient identification platforms to prevent medical identity theft. Biometric patient identity management platforms are also effective in eliminating duplicate records and overlays. Usually, such platforms use patients’ biometric characteristics, such as iris patterns or fingerprints to lock and encrypt their medical records. If anyone wants to access their medical record, the platform uses a camera, webcam, or fingerprint scanner to scan the individual’s biometric data to verify against the registered data. This method has proven effective in preventing unauthorized individuals from accessing someone’s medical record.
Routine HIPAA Training
On many occasions, electronic health records can be compromised due to internal factors, such as lack of proper awareness around HIPAA compliance by employees. HIPAA training is not just a compliance requirement: it helps employees to understand the importance of protecting electronic health records and how to handle sensitive patient data. Conducting HIPAA training regularly does not need to be a burdensome task. With HIPAA Ready, you will be able to streamline the training process and satisfy HIPAA training requirements effortlessly.
Maintaining and Monitoring Audit Logs
If your company stores or access patient information in any way, you should also have the means to produce and maintain a log report to provide you with details of who accessed the patient data, the time of access, and the types of data that were accessed. These log reports help you to ensure that employees are only accessing data that are required to perform their job functions. Audit logs also can help you check if any inappropriate or unauthorized access is occurring or not.
An important feature of HIPAA Ready is that the application enables users to maintain an audit log and have a clear overview of all the HIPAA policies, procedures and updates.
Security Controls for Bring Your Own Device (BYOD)
Bring Your Own Device (BYOD) policies have been gaining popularity in the healthcare industry, but they bring significant risks. Healthcare organizations must ensure that they have appropriate security controls, rules, procedures, practices, and technology in place to protect electronic health records when they are accessed from personal devices.
Oftentimes, you will hear news about a healthcare provider being penalized for stolen devices that contained personal health information. This is why organizations need to develop clear policies and procedures regarding the usage of personal devices.
With HIPAA Ready, you can add, edit, and update policies and procedures and notify relevant individuals across the organization. You can also maintain a log for all electronic protected health information (ePHI) containing devices and to whom the devices are assigned.
Ensure Continuous Compliance with HIPAA Ready
HIPAA Ready is a robust, cloud-based HIPAA compliance management application that combines all seven compliance management modules and lets you streamline your compliance efforts from a single centralized platform.
Interested in learning more about HIPAA Ready? Leave a comment below!